Cyber Resilience Tested: How Transport for London Thwarted a High-Stakes Cyberattack on Urban Transit Systems
Transport for London (TfL), the government body responsible for the transport system in Greater London, recently confronted a significant cybersecurity incident, underscoring the escalating threats facing critical infrastructure systems worldwide. This incident, characterized by sophisticated and persistent cyberattacks, highlights the vulnerabilit
FBI’s High-Stakes Digital Breakthrough: Cracking Encrypted Phones and the Battle Between Privacy and Security
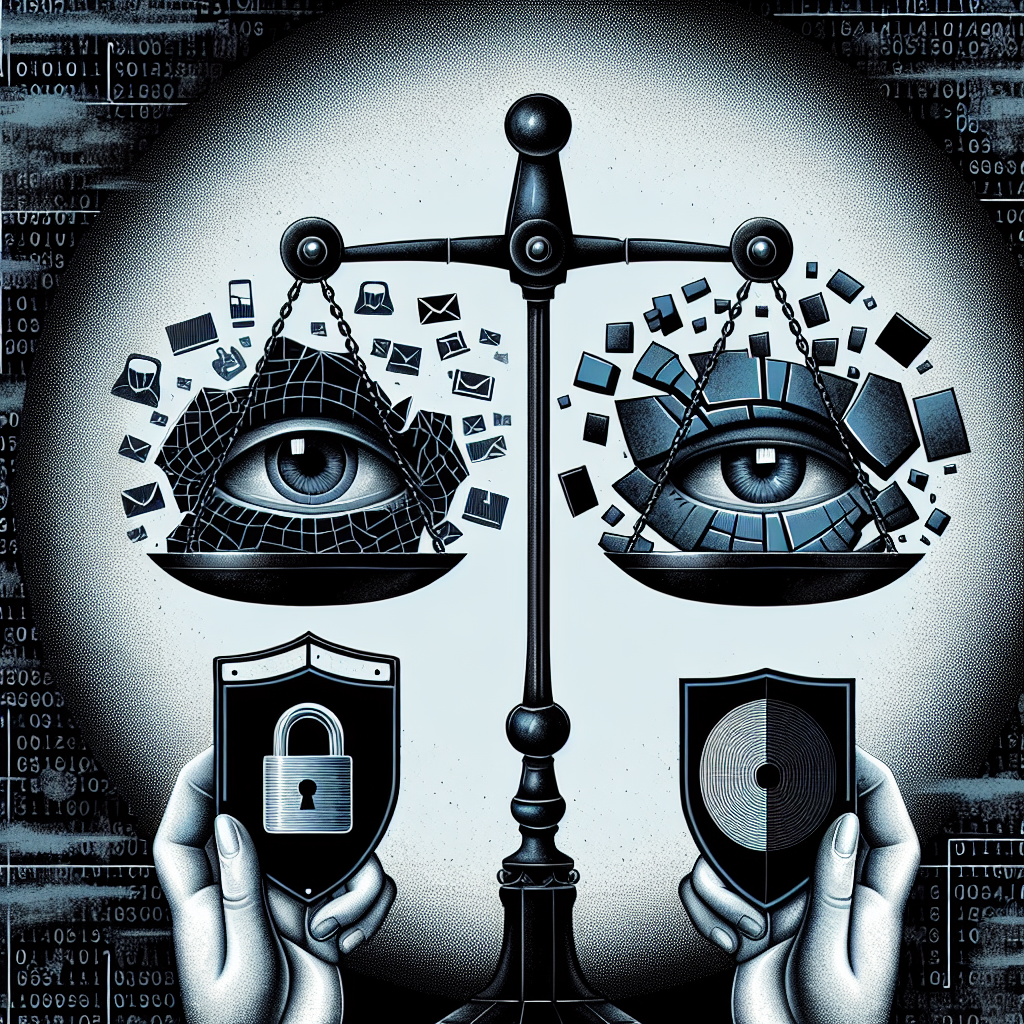
In a recent high-profile case, the FBI successfully gained access to the mobile phone of Thomas Matthew Crooks, the suspect involved in an assassination attempt on former President Donald Trump during a rally. This development underscores the intricate intersection between law enforcement and cybersecurity, highlighting both the capabilities and co
Surge in DDoS Attacks on French Websites Exposes Cybersecurity Risks for Paris Olympics

Recent developments in cyber warfare have seen a surge in Distributed Denial of Service (DDoS) attacks targeting French websites, highlighting potential risks for the upcoming Paris Olympics. Authorities and cybersecurity experts are closely observing these activities, which are largely attributed to hacktivist groups People’s Cyber Army and Hackne
Cybersecurity in Crisis: The Ripple Effects of CrowdStrike’s Outage on Critical Infrastructure and Beyond

The recent widespread outage experienced by CrowdStrike has cast a significant spotlight on the vulnerabilities that can beset even the most robust cybersecurity solutions. Enterprises around the globe rely heavily on continuous and seamless access to cybersecurity services, highlighting why the CrowdStrike incident has had such a profound impact a
CDK Global Cyberattack: Ongoing Disruptions at Car Dealerships Worsen

CDK Global, a prominent provider of software solutions for car dealerships, is facing severe operational challenges due to a recent cyberattack. The attack has disrupted the activities of approximately 15,000 dealerships across North America, forcing many to revert to manual processes and causing significant business interruptions.
U.S. Commerce Department Prohibits Kaspersky Software for U.S. Customers
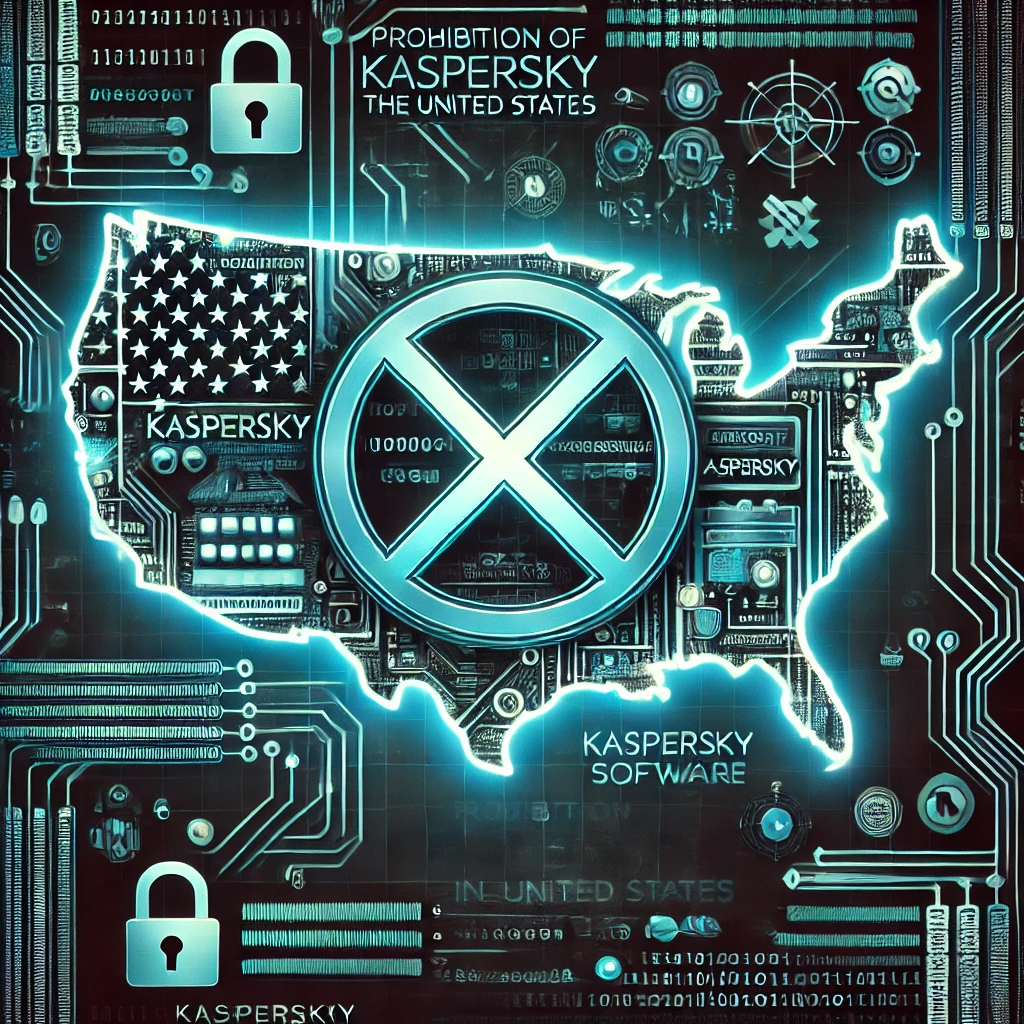
The U.S. Department of Commerce has made a significant move by prohibiting Kaspersky Lab, Inc., a subsidiary of the Russian cybersecurity company Kaspersky Lab, from providing its software and services to U.S. customers. This action is part of the broader efforts to safeguard national security and protect sensitive information from foreign threats.
Pegasus Emerges as a Cyber Trojan Horse Attacking Press Freedom and Personal Liberties Across Europe

Pegasus spyware has emerged as a significant threat targeting journalists and opposition figures, with recent incidents highlighting its use against Russian- and Belarusian-speaking media based in Europe. This spyware, developed by the NSO Group, is known for allowing operators extensive access to targets’ devices, enabling them to retrieve message
Polyfill Supply Chain Breach: A Wake-Up Call for Strengthening Third-Party Security Measures

A recent cyber incident has highlighted the vulnerabilities inherent in supply chain attacks, with the Polyfill JavaScript library found to be at the center of an extensive security breach. This incident has impacted over 100,000 websites, showcasing the broad-reaching implications and the sophisticated nature of modern cyber threats.
Supply chain
Awareness
AWARE NESS
What we do
CASE STUDIES CASE STUDIES Welcome to our case studies section, where we showcase real-world examples of our strategies in action. Each case study highlights the challenges faced, solutions implemented, and the positive outcomes achieved. These examples demonstrate the practical impact of our methods across various industries, offering valuable insights and actionable lessons. Explore these success […]